Guide to Fraud Prevention, Part 1: Hardware
Leverage sophisticated hardware systems to protect yourself and your business from real estate fraud.

Tom Cronkright
3 miins
Fraud Prevention
Jul 19, 2021
Apr 22, 2026
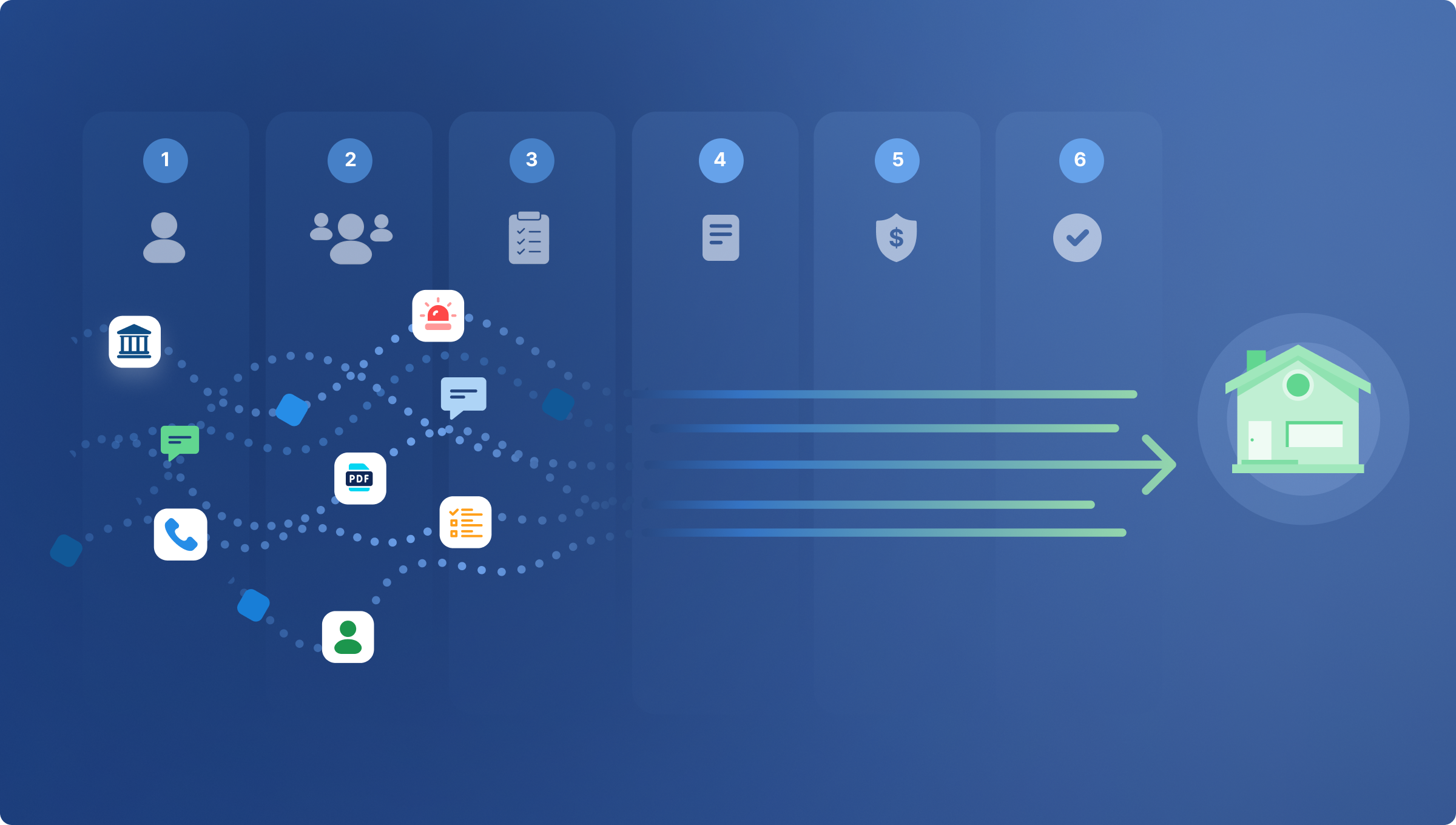
You know online fraud exists. You see it in the headlines every day. Scammers target even the most savvy industry leaders with increasingly complex methods. They use artificial intelligence (AI) and machine learning to accelerate their attacks on small firms and large financial institutions alike. So what can you do to protect yourself and your business? We compiled this expert four-part guide on how to proactively prevent fraud, based on emerging policy and best practice, first-hand experience with fraud tactics, and analysis of the latest data.
Learn the practical steps you can take to disrupt fraud and strengthen your business across these four pillars of fraud prevention: (1) Hardware, (2) Software, (3) Procedure, and (4) People.
Table of Contents
- Hardware: Foundation for Fraud Prevention
- Perimeter Security Hardware
- Network Security Hardware
- Systems Monitoring
- Hardware Infrastructure
Hardware: Foundation for Fraud Prevention
First up: hardware, the root of a sophisticated fraud prevention strategy. The most secure businesses start with the physical connections that enable their services. All other cybersecurity measures draw their effectiveness from this strong foundation. Purchasing secure hardware is an up-front investment, but it can pay dividends with years of loss prevention when you prioritize secure systems. Although there will be updates and additions over the life of your hardware, it will largely remain stable, even as software, personnel, and scams evolve. When you invest in secure infrastructure, you’ll pave the way for prolonged stability and business growth.
Learn which hardware and tactics keep your business data and communications fraud-proof.
Perimeter Security Hardware
Think of a castle. Around the entire perimeter of its thick stone walls is a moat with a drawbridge, enabling close control of traffic coming and going. The drawbridge rolls up at the first sign of a threat and the moat prevents attackers from even reaching the fortification. Similarly, perimeter security, including a firewall and other forms of fraud detection, monitors your ingoing and outgoing web traffic and secures your systems against any unusual patterns that could indicate that you’re being targeted for data breaches or fraudulent activities.
Invest in an advanced perimeter security system, such as Cisco or Watchguard. Any perimeter security hardware you acquire should have the following features:
- Web-Content Filtering
- Anti-Virus Scanning
- Reputation, Application and Protocol Protection
- Advanced Threat Protection for Zero-Day Exploits
- Data Loss Prevention and Auditing Policies
- Geolocation Blocking
These kinds of perimeter security systems come with a subscription to a threat database that’s always up to date with the latest scams, viruses, and malware. Patches will automatically deploy to protect your customers’ sensitive information–from bank account information to social security numbers–against new threats in the database.
Network Security Hardware
You might think of your business’s wireless network as a bridge to your clients, but cybercriminals try to use it as a bridge leading straight to the most sensitive data and vulnerable aspects of your business.
Prevent scammers from exploiting your WiFi by partitioning your main wireless network and guest network. Create a separate network for guests to use so that any malware introduced on the public network won’t contaminate your business network or any of the smart devices connected to it. This can typically be accomplished by adjusting your router settings, without ever needing to lay a new cable.
Add an additional layer of security by adopting wireless intrusion prevention, which prevents multiple attempts at guessing passwords. And finally, implement identity-based 802.1x authentication, the industry standard way to verify the identities of your WiFi users and prevent account takeover, advanced by the Institute of Electrical and Electronics Engineers.
Want a deeper dive? Get our free guide to cybersecurity measures.
Systems Monitoring
If your perimeter security system and firewall are the moat surrounding your castle, think of systems monitoring as the sentry at the gate, ready to alert you to any potential intruder. You need a separate computer on your network dedicated to fraud detection. Set up this device in direct communication with the firewall so that it alerts you with a text or email message when something unusual occurs.
Not all suspicious activity is a legitimate threat, so many notifications will be false alarms, especially when your system is new. Over time, as you gather more data, you can adjust the alerts settings and train your systems to distinguish between business as usual and fraudulent transactions.
Hardware Infrastructure
Life happens. Hardware fails. The power goes out. A file is deleted. For those times when things don’t go as planned, you need a redundant, robust, and encrypted backup strategy that utilizes the 3-2-1 rule.
Let’s break down what that means:
- Redundant – Identical functions performed by multiple pieces of equipment so if one fails, you’ll have the same service or storage performed by another.
- Encrypted – Your data should be encrypted so that even if someone gets direct physical access to a hard drive, it will be meaningless to them.
- Robust – System settings that ensure encrypted information only reaches authorized recipients and still remains anonymous and confidential.
- 3-2-1 rule – 3 copies of your data (the original and 2 backups), backed up on at least 2 different types of storage, with at least 1 copy of your data stored offsite.
These safeguards ensure that your business and clients are secure even when accidents happen. Criminals tend to strike while you’re busy dealing with the latest crisis, but they won’t succeed when faced with complex, layered fraud prevention infrastructure.
Investing in multiple lines of hardware defense requires research and investment, but is the easy choice relative to high-cost, high-stakes recovery from a vicious cyber attack.
Now that you’ve secured your hardware against fraud, learn how to secure your software in the second part of our series. Get the full guide to master all four pillars of fraud prevention:
FAQ
Co-founder & Executive Chairman
Tom Cronkright is the Executive Chairman of CertifID, a technology platform designed to safeguard electronic payments from fraud. He co-founded the company in response to a wire fraud he experienced and the rising instances of real estate wire fraud. He also serves as the CEO of Sun Title, a leading title agency in Michigan. Tom is a licensed attorney, real estate broker, title insurance producer and nationally recognized expert on cybersecurity and wire fraud.
You know online fraud exists. You see it in the headlines every day. Scammers target even the most savvy industry leaders with increasingly complex methods. They use artificial intelligence (AI) and machine learning to accelerate their attacks on small firms and large financial institutions alike. So what can you do to protect yourself and your business? We compiled this expert four-part guide on how to proactively prevent fraud, based on emerging policy and best practice, first-hand experience with fraud tactics, and analysis of the latest data.
Learn the practical steps you can take to disrupt fraud and strengthen your business across these four pillars of fraud prevention: (1) Hardware, (2) Software, (3) Procedure, and (4) People.
Table of Contents
- Hardware: Foundation for Fraud Prevention
- Perimeter Security Hardware
- Network Security Hardware
- Systems Monitoring
- Hardware Infrastructure
Hardware: Foundation for Fraud Prevention
First up: hardware, the root of a sophisticated fraud prevention strategy. The most secure businesses start with the physical connections that enable their services. All other cybersecurity measures draw their effectiveness from this strong foundation. Purchasing secure hardware is an up-front investment, but it can pay dividends with years of loss prevention when you prioritize secure systems. Although there will be updates and additions over the life of your hardware, it will largely remain stable, even as software, personnel, and scams evolve. When you invest in secure infrastructure, you’ll pave the way for prolonged stability and business growth.
Learn which hardware and tactics keep your business data and communications fraud-proof.
Perimeter Security Hardware
Think of a castle. Around the entire perimeter of its thick stone walls is a moat with a drawbridge, enabling close control of traffic coming and going. The drawbridge rolls up at the first sign of a threat and the moat prevents attackers from even reaching the fortification. Similarly, perimeter security, including a firewall and other forms of fraud detection, monitors your ingoing and outgoing web traffic and secures your systems against any unusual patterns that could indicate that you’re being targeted for data breaches or fraudulent activities.
Invest in an advanced perimeter security system, such as Cisco or Watchguard. Any perimeter security hardware you acquire should have the following features:
- Web-Content Filtering
- Anti-Virus Scanning
- Reputation, Application and Protocol Protection
- Advanced Threat Protection for Zero-Day Exploits
- Data Loss Prevention and Auditing Policies
- Geolocation Blocking
These kinds of perimeter security systems come with a subscription to a threat database that’s always up to date with the latest scams, viruses, and malware. Patches will automatically deploy to protect your customers’ sensitive information–from bank account information to social security numbers–against new threats in the database.
Network Security Hardware
You might think of your business’s wireless network as a bridge to your clients, but cybercriminals try to use it as a bridge leading straight to the most sensitive data and vulnerable aspects of your business.
Prevent scammers from exploiting your WiFi by partitioning your main wireless network and guest network. Create a separate network for guests to use so that any malware introduced on the public network won’t contaminate your business network or any of the smart devices connected to it. This can typically be accomplished by adjusting your router settings, without ever needing to lay a new cable.
Add an additional layer of security by adopting wireless intrusion prevention, which prevents multiple attempts at guessing passwords. And finally, implement identity-based 802.1x authentication, the industry standard way to verify the identities of your WiFi users and prevent account takeover, advanced by the Institute of Electrical and Electronics Engineers.
Want a deeper dive? Get our free guide to cybersecurity measures.
Systems Monitoring
If your perimeter security system and firewall are the moat surrounding your castle, think of systems monitoring as the sentry at the gate, ready to alert you to any potential intruder. You need a separate computer on your network dedicated to fraud detection. Set up this device in direct communication with the firewall so that it alerts you with a text or email message when something unusual occurs.
Not all suspicious activity is a legitimate threat, so many notifications will be false alarms, especially when your system is new. Over time, as you gather more data, you can adjust the alerts settings and train your systems to distinguish between business as usual and fraudulent transactions.
Hardware Infrastructure
Life happens. Hardware fails. The power goes out. A file is deleted. For those times when things don’t go as planned, you need a redundant, robust, and encrypted backup strategy that utilizes the 3-2-1 rule.
Let’s break down what that means:
- Redundant – Identical functions performed by multiple pieces of equipment so if one fails, you’ll have the same service or storage performed by another.
- Encrypted – Your data should be encrypted so that even if someone gets direct physical access to a hard drive, it will be meaningless to them.
- Robust – System settings that ensure encrypted information only reaches authorized recipients and still remains anonymous and confidential.
- 3-2-1 rule – 3 copies of your data (the original and 2 backups), backed up on at least 2 different types of storage, with at least 1 copy of your data stored offsite.
These safeguards ensure that your business and clients are secure even when accidents happen. Criminals tend to strike while you’re busy dealing with the latest crisis, but they won’t succeed when faced with complex, layered fraud prevention infrastructure.
Investing in multiple lines of hardware defense requires research and investment, but is the easy choice relative to high-cost, high-stakes recovery from a vicious cyber attack.
Now that you’ve secured your hardware against fraud, learn how to secure your software in the second part of our series. Get the full guide to master all four pillars of fraud prevention:
Co-founder & Executive Chairman
Tom Cronkright is the Executive Chairman of CertifID, a technology platform designed to safeguard electronic payments from fraud. He co-founded the company in response to a wire fraud he experienced and the rising instances of real estate wire fraud. He also serves as the CEO of Sun Title, a leading title agency in Michigan. Tom is a licensed attorney, real estate broker, title insurance producer and nationally recognized expert on cybersecurity and wire fraud.
Sign up for The Wire to join the conversation.