Business Email Compromise Attack: CEO's Hacked Email Account Results in $3M in Stolen Funds
The email came directly from Mattel CEO Christopher Sinclair, telling his employee to wire $3 million to a new vendor.
.jpg)
Tyler Adams
4 mins
Scams
Jul 19, 2021
Apr 22, 2026
An important note to our readers: since this article’s publication, we’ve acquired new data that further emphasizes the seriousness of this topic. Please read our additional post on the topic here: FBI PSA Warns About the RIse in Business Email Compromise.
The email came directly from Mattel CEO Christopher Sinclair, telling his employee to wire $3 million to a new vendor. Anxious to be responsive to a new boss, the employee did just that. Except the email didn’t come from Sinclair. His email had been hacked by scammers posing as him and waiting to rake in the cash.
This kind of scam, called Business Email Compromise (BEC) or CEO fraud, is a type of phishing attack that is proving to be a big headache to businesses of all sizes. The FBI began tracking BEC losses in October 2013. In 2023, they recorded nearly $2.9 billion in reported losses from 21,489 complaints, accounting for 23% of all reported cybercrime losses. Today, the FBI estimated business email compromise to be a $50B scam.
How do fraudsters commit Business Email Compromise (BEC)?
In a BEC attack, cyber thieves hack into or spoof legitimate business e-mail accounts — using social engineering techniques or other fraudulent means — in order to steal large amounts of money.
Once fraudsters have impersonated a key personnel’s email address, they can send messages to financial staff and fool them into making payments.
From the perspective of the financial department, the money transfer looks completely legitimate; however, the payment has landed straight into the scammer’s account.
Unlike the traditional types of phishing, which tend to target an extensive number of people, CEO fraud is very focused. Fraudsters will do their homework to get as much information as possible about the target personnel in a company. For example, they will scour employees compromised email accounts, assess recent company news, and study the target’s routine on social media sites.
After gathering all the necessary information, scammers then establish a way of emailing the fraudulent funds transfer request in a manner that looks convincing and difficult to detect. If the cyber criminals have compromised a key personnel’s email account, they can develop techniques for avoiding detection, such as setting up inbox rules to redirect or delete certain messages, or editing the “Reply to” addresses so that emails cannot go to the legitimate recipients.
If they fail to compromise a key personnel’s email account, they can create a look-alike email address (a “spoofed” email address). By trading a hyphen for an underscore or reversing letters in an anagram, they can easily create an email that would pass for the real thing.
How is a Business Email Compromise Scam carried out?
After a fraudster has successfully spear-phished a email account, a BEC attack normally takes any of the following five types:
1. CEO fraud
This is the most common type of BEC attack. Once fraudsters have managed to hack or spoof a CEO’s email address, they then send an email from the “CEO” to a subordinate staff responsible for processing funds requests, with instructions on where to make the payments.
To succeed in this type of attack, cyber criminals usually include a sense of urgency to prevent an employee from making further clarifications about the request. For example, they can include a note that it’s an emergency and the money is required as soon as possible.
2. Bogus invoice scam
In this scenario, fraudsters attempt to imitate invoices and accounts, and direct payments to their own bank accounts.
For example, cyber criminals can hack into an executive’s email account, look for a vendor invoice or bill that is about to be paid, and then cunningly email the finance department with altered details about where to send the payment.
3. Attorney impersonation scam
In this scheme, a cyber criminal first impersonates a company’s law firm, and then sends an email requesting a colossal amount of money to assist in meeting the costs of a legal dispute, settling a bill, or completing a secret company acquisition.
The fraudster will convince the target of the confidentiality and time-sensitivity of the issue, which discourage the employee from making further confirmations.
4. Bank account compromise attack
Just like the bogus invoice scam, this type of attack occurs when a fraudster gains entry into a company’s email account and then sends messages to customers with details of modified bank account details (which belongs to the hacker).
5. Data theft attack
Instead of stealing cash, thieves sometimes want information instead. Data theft takes place when fraudsters have compromised an executive’s email account and request the finance or HR department to send them confidential company documents. This type of attack is normally used as the stepping stone for a more extensive and destructive cyber - attack.
Why is BEC such a big problem?
Not long ago, email phishing and spear-phishing attacks were easy to recognize. The lucky lottery win and other scamming messages sent to potential victims personal and business email inboxes were easy to avoid. Now, fraudsters have evolved and use very sophisticated, difficult-to-detect techniques.
Because of the lucrative nature of BEC attack, it attracts a large number of cybercriminals. A successful BEC exploit can lead to a net payoff of about $140,000 per incident, according to The SSL Store, while other types of attacks, like ransomware, result in a lower net payoff of about $30,000. In recent years, some notable companies around the world have experienced huge losses due to BEC attacks.
BEC attackers will continue to grow and perfect their tradecraft. With such a numbers of criminals launching increasingly sophisticated attacks, investing in email security and fraud prevention is a must for every business.
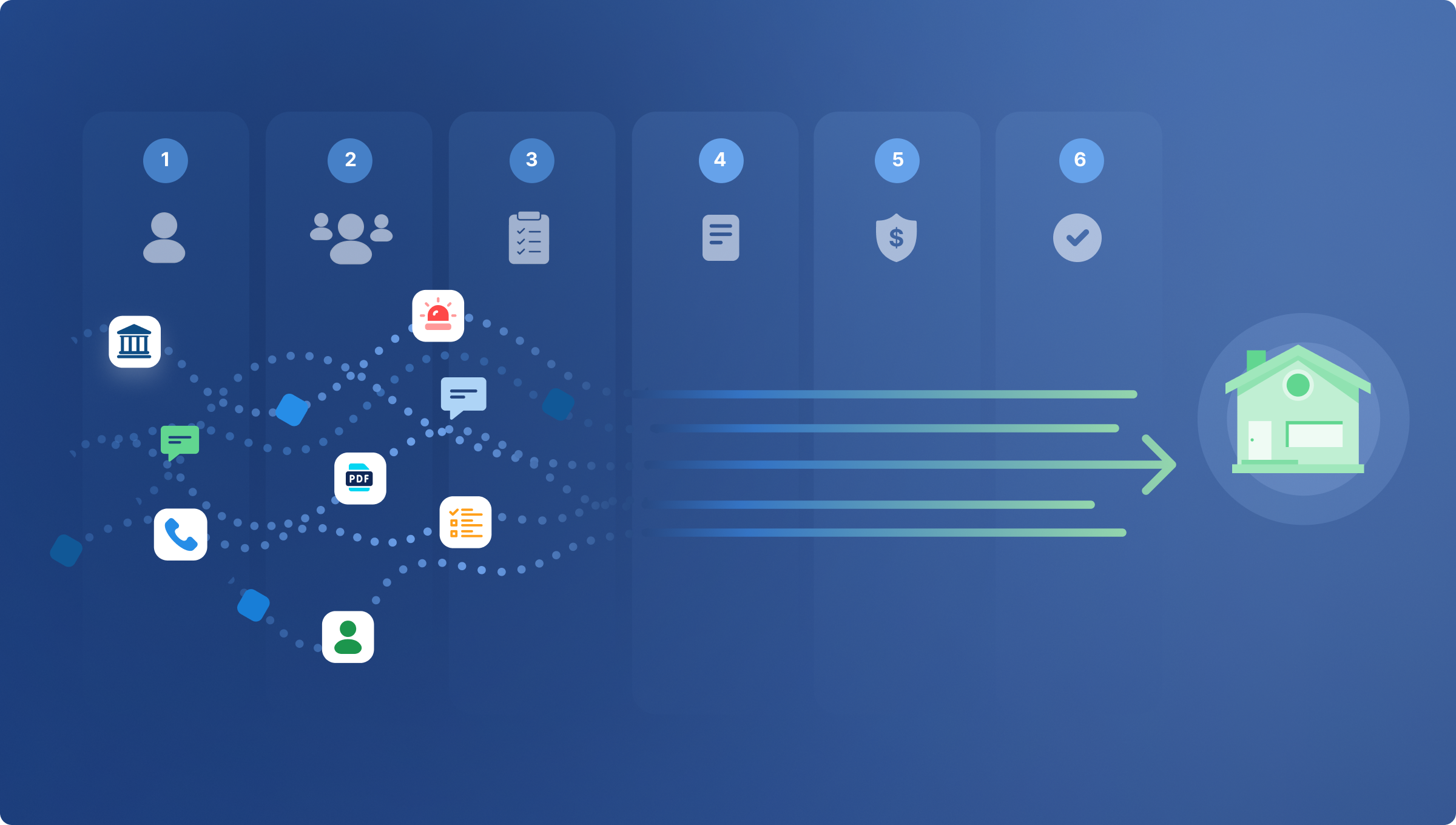
If you're concerned about business email compromise and the potential losses at your business due to wire transfer fraud, learn how CertifID can protect your funds.
.png)
FAQ
Co-founder & CEO
Tyler brings a decade of leadership experience developing and launching technology businesses. Before co-founding CertifID, Tyler led new product development at BCG Digital Ventures for Mercedes-Benz, First American Financial, Boston Scientific, and Aflac.
An important note to our readers: since this article’s publication, we’ve acquired new data that further emphasizes the seriousness of this topic. Please read our additional post on the topic here: FBI PSA Warns About the RIse in Business Email Compromise.
The email came directly from Mattel CEO Christopher Sinclair, telling his employee to wire $3 million to a new vendor. Anxious to be responsive to a new boss, the employee did just that. Except the email didn’t come from Sinclair. His email had been hacked by scammers posing as him and waiting to rake in the cash.
This kind of scam, called Business Email Compromise (BEC) or CEO fraud, is a type of phishing attack that is proving to be a big headache to businesses of all sizes. The FBI began tracking BEC losses in October 2013. In 2023, they recorded nearly $2.9 billion in reported losses from 21,489 complaints, accounting for 23% of all reported cybercrime losses. Today, the FBI estimated business email compromise to be a $50B scam.
How do fraudsters commit Business Email Compromise (BEC)?
In a BEC attack, cyber thieves hack into or spoof legitimate business e-mail accounts — using social engineering techniques or other fraudulent means — in order to steal large amounts of money.
Once fraudsters have impersonated a key personnel’s email address, they can send messages to financial staff and fool them into making payments.
From the perspective of the financial department, the money transfer looks completely legitimate; however, the payment has landed straight into the scammer’s account.
Unlike the traditional types of phishing, which tend to target an extensive number of people, CEO fraud is very focused. Fraudsters will do their homework to get as much information as possible about the target personnel in a company. For example, they will scour employees compromised email accounts, assess recent company news, and study the target’s routine on social media sites.
After gathering all the necessary information, scammers then establish a way of emailing the fraudulent funds transfer request in a manner that looks convincing and difficult to detect. If the cyber criminals have compromised a key personnel’s email account, they can develop techniques for avoiding detection, such as setting up inbox rules to redirect or delete certain messages, or editing the “Reply to” addresses so that emails cannot go to the legitimate recipients.
If they fail to compromise a key personnel’s email account, they can create a look-alike email address (a “spoofed” email address). By trading a hyphen for an underscore or reversing letters in an anagram, they can easily create an email that would pass for the real thing.
How is a Business Email Compromise Scam carried out?
After a fraudster has successfully spear-phished a email account, a BEC attack normally takes any of the following five types:
1. CEO fraud
This is the most common type of BEC attack. Once fraudsters have managed to hack or spoof a CEO’s email address, they then send an email from the “CEO” to a subordinate staff responsible for processing funds requests, with instructions on where to make the payments.
To succeed in this type of attack, cyber criminals usually include a sense of urgency to prevent an employee from making further clarifications about the request. For example, they can include a note that it’s an emergency and the money is required as soon as possible.
2. Bogus invoice scam
In this scenario, fraudsters attempt to imitate invoices and accounts, and direct payments to their own bank accounts.
For example, cyber criminals can hack into an executive’s email account, look for a vendor invoice or bill that is about to be paid, and then cunningly email the finance department with altered details about where to send the payment.
3. Attorney impersonation scam
In this scheme, a cyber criminal first impersonates a company’s law firm, and then sends an email requesting a colossal amount of money to assist in meeting the costs of a legal dispute, settling a bill, or completing a secret company acquisition.
The fraudster will convince the target of the confidentiality and time-sensitivity of the issue, which discourage the employee from making further confirmations.
4. Bank account compromise attack
Just like the bogus invoice scam, this type of attack occurs when a fraudster gains entry into a company’s email account and then sends messages to customers with details of modified bank account details (which belongs to the hacker).
5. Data theft attack
Instead of stealing cash, thieves sometimes want information instead. Data theft takes place when fraudsters have compromised an executive’s email account and request the finance or HR department to send them confidential company documents. This type of attack is normally used as the stepping stone for a more extensive and destructive cyber - attack.
Why is BEC such a big problem?
Not long ago, email phishing and spear-phishing attacks were easy to recognize. The lucky lottery win and other scamming messages sent to potential victims personal and business email inboxes were easy to avoid. Now, fraudsters have evolved and use very sophisticated, difficult-to-detect techniques.
Because of the lucrative nature of BEC attack, it attracts a large number of cybercriminals. A successful BEC exploit can lead to a net payoff of about $140,000 per incident, according to The SSL Store, while other types of attacks, like ransomware, result in a lower net payoff of about $30,000. In recent years, some notable companies around the world have experienced huge losses due to BEC attacks.
BEC attackers will continue to grow and perfect their tradecraft. With such a numbers of criminals launching increasingly sophisticated attacks, investing in email security and fraud prevention is a must for every business.
If you're concerned about business email compromise and the potential losses at your business due to wire transfer fraud, learn how CertifID can protect your funds.
.png)
Co-founder & CEO
Tyler brings a decade of leadership experience developing and launching technology businesses. Before co-founding CertifID, Tyler led new product development at BCG Digital Ventures for Mercedes-Benz, First American Financial, Boston Scientific, and Aflac.
Sign up for The Wire to join the conversation.